Checking Certificate Expiration
When using RPG API Express to connect to a web service via SSL, you might receive one of the following error messages:
- "Error during initializing SSL. The value specified for the argument is not correct. RC(24) errno(3021)"
- "Error performing SSL handshake. There is no error. RC(24-) errno(0)"
This error frequently indicates that one or more certificates have expired. Due to how IBM handles certificates, any expired certificate can cause this error to occur, even if the expired certificate is for an entirely different web service.
The easiest way to resolve this or eliminate it as a possible cause is to check if any certificates have expired, and either replace or remove them.
This guide shows the process using the new DCM interface. For instructions using heritage DCM, click here.
Accessing DCM
#To begin, verify that the *ADMIN HTTP server job is running with the following command:
WRKSBSJOB SBS(QHTTPSVR)
If you don't see *ADMIN in the list, please run the following command to start it:
STRTCPSVR SERVER(*HTTP) HTTPSVR(*ADMIN)
After you've ensured that the *ADMIN server is running, open a web browser, and go to http://YourIBMIPAddress:2006/dcm/ - you should see a login page as seen below:
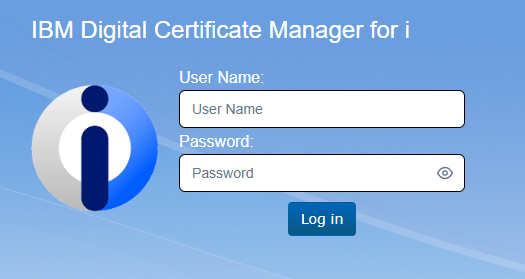
You will want to log in to DCM using a profile with elevated permissions.
Open the *SYSTEM certificate store by first clicking on the "Open Certificate Store" link under the Actions header, then select *SYSTEM:
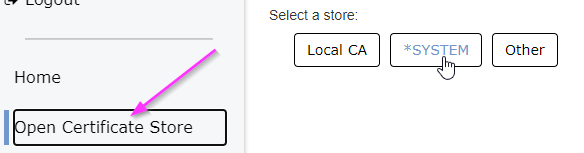
Enter your *SYSTEM store password when prompted and click "open".
Viewing Expired Certificates
#The main *SYSTEM certificate store page will load and show a list of install certificates. At the top of the list will be a filter for "Server/Client Certificate":
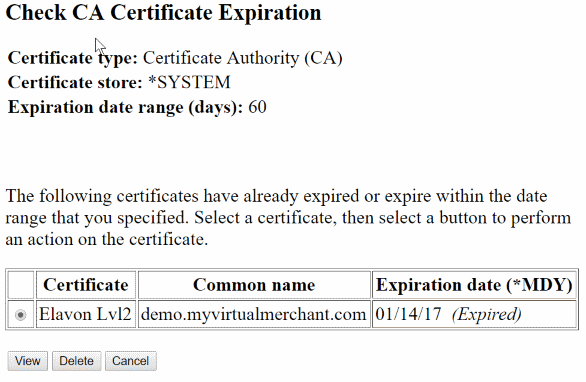
Click the "x" to remove that filter.
After removing the filter, you should now see a full list of all installed certificates:
The certificates are displayed as cards with their expiration information, and they are color-coded so that any certificates that are expired or are expiring soon are highlighted:
In this example, we can see:
- The Payeezy certificate in the center of the bottom row is expiring in 4767 days, so it is not shaded
- The Cloudflare certificate at the left of the top row is expiring soon - in 5 days - so it is shaded yellow
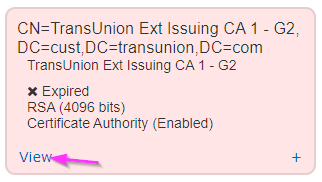
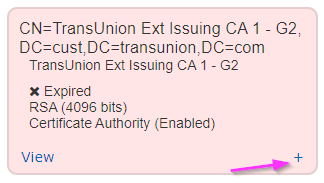
- The TransUnion certificate at the right of the bottom row has expired, so it is shaded red
Once you've identified an expired certificate, you can click the "View" link on the card to go to that certificate directly for more information:
This is especially helpful for Server/Client certificates if you need to check what SSL applications they are assigned to, so that they can be replaced before removing them.
Removing Expired Certificates
#When it comes time to remove expired certificates, there are two ways to do so.
Using the Certificate Detail Page
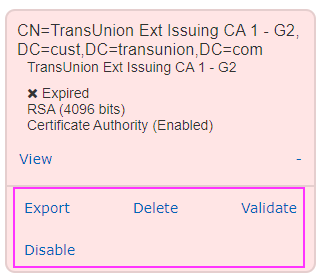
#From the detail page of the certificate, there are four actions listed at the top:
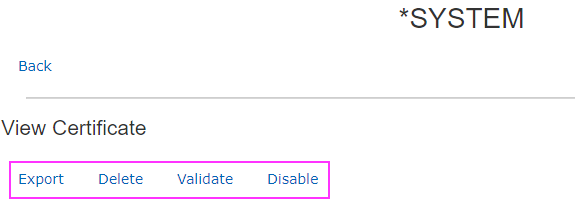
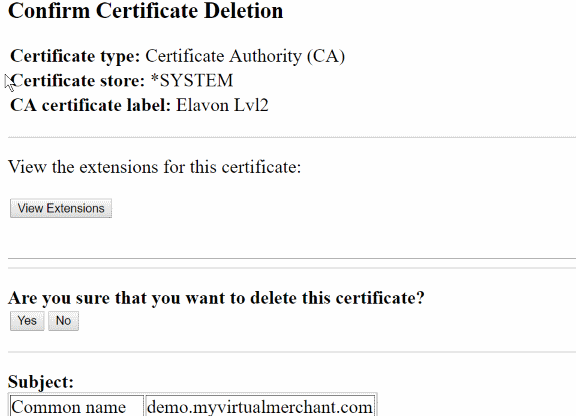
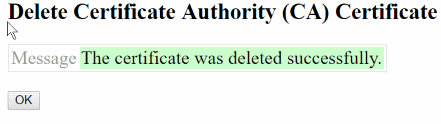
You can select "Delete" to permanently remove the certificate, or "Disable" to make the certificate unavailable (useful for testing before deleting).
From the Certificate Card List
#Find the certificate you want to delete and press the "+" button at the bottom right of the card:
This will open a panel with the four actions available on the certificate page shown in step 1. Select either "Delete" or "Disable" as appropriate: